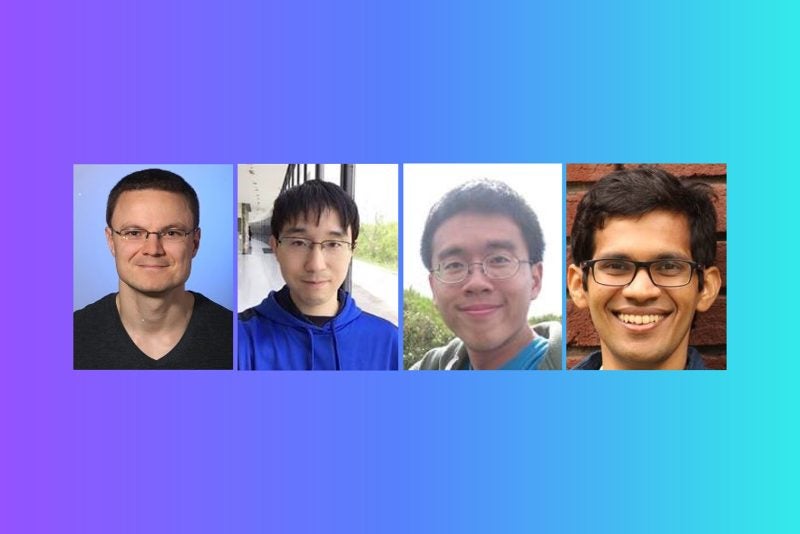
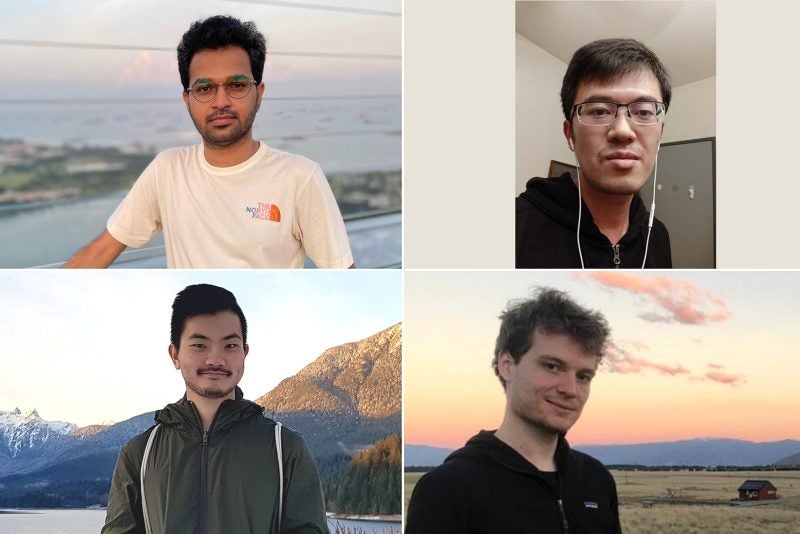
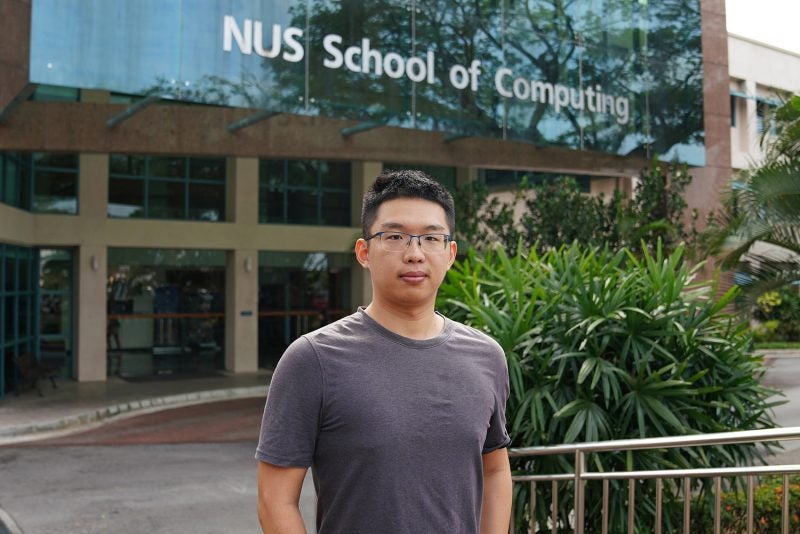
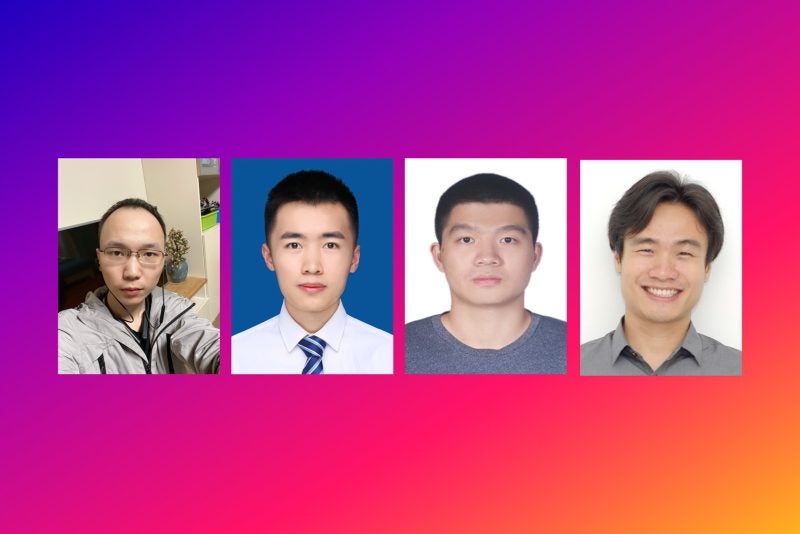
20 November 2020 – Computer Science professors Chan Mun Choon and Han Jun, along with their PhD students Nishant Budhdev and Nitya Lakshmanan, were recently listed in the GSMA Mobile Security Hall of Fame.
The Hall of Fame recognises those who have made contributions to increasing the security of the mobile industry, through uncovering significant system vulnerabilities.
The team, along with former NUS Computing assistant professor Kang Min Suk, were acknowledged for discovering a new security vulnerability involving mobile phones.
The potential attack, named ‘Stealthy Location Identification Attack exploiting Carrier Aggregation’ (or SLIC in short) can track the location of target cellular user devices in the modern Long-Term Evolution (LTE) cellular network.
In comparison to existing location privacy attacks that can only infer coarse-grained location information, or require the installation of malware on victims’ phones, SLIC is able to achieve fine-grained location tracking of targeted cellular user devices in a passive manner.
This means that SLIC is not only able to accurately identify a target user’s walking path while in an indoor, multi-story building environment, it does so without requiring any malware on the user’s phone.
The attack works through exploiting a subtle ‘side-channel’ in the LTE cellular network, using a feature known as carrier aggregation (CA).
Traditionally, cellular network users are served by a single base station, known as a primary cell. With CA, users are not only connected to a primary cell for control messaging, but also to one or more additional base stations, known as secondary cells, to achieve higher data rates.
The side-channel that SLIC exploits is the number of activated secondary cells that are connected to each user’s device.
“We discovered that a passive adversary can learn this side-channel information, namely, the number of actively transmitting base stations for any user of interest,” said Lakshmanan.
“A time series of this side-channel information can constitute a highly unique fingerprint of a walking path, which can then be used to identify the path taken by a target cellular user,” she added.
Each path exhibits a highly unique fingerprint as the physical environment (such as building architecture) that surrounds each walking path affects the radio-frequency signal quality at each location on the path.
Therefore, if an adversary records a fingerprint of a specific path in advance, they will be able to accurately predict the likelihood of a target user walking the same path.
“The experiments we did demonstrated the collection of side-channel information to form a small-scale path identification attack in an existing LTE-A cellular network. This shows that SLIC is feasible in current cellular networks,” said Lakshmanan.
She added that while the team’s work probably stood out because they were able to highlight a potential security threat before widespread 5G network deployment, they were “pleasantly surprised” to be listed in the hall of fame.
“It’s an acknowledgement of the impact of our work. I’d like to give special thanks to PhD students Raj and Soundarya, who helped us during the initial feasibility test phase, and Daryl, who helped us with the data collection as a final year undergraduate student,” said Lakshmanan.